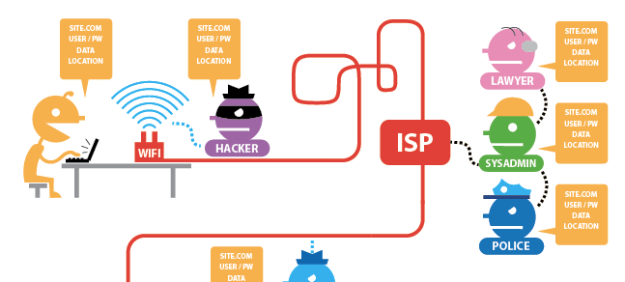
The EFF have an interactive graphic which shows you what information can be grabbed when you’re using Tor or HTTPS
Home secretary Theresa May wants to be able to connect IP addresses (which identify machines) with users (those using it at that particular time).
In a nutshell this means being able to identify whether you were in a particular place at a particular time – only the ‘place’ in question happens to be virtual: a website.
Now clearly this is aimed at identifying terrorists and paedophiles. But then so was RIPA, a law which has been used to spy on journalists and intimidate staff who speak to them and to “pull reporters’ phone records in every single leak inquiry in the last ten years“, including all calls to the Sun’s newsdesk and by their political editor in one inquiry.
In recent weeks we have heard about prison officials monitoring confidential phonecalls between MPs and prisoners, and between lawyers and their clients.
We have heard that police store information on journalists ranging from their sexual orientation to things that they have tweeted about.
We have heard that mobile phone companies use automated systems that allow police and others with access to get customer data “like a cash machine”. O2 was the only major phone network that even reviewed requests.
And when it comes to communications data we have heard that GCHQ also accessed that information without a warrant.
It’s not just public bodies either. While the newspaper hacking scandal was being investigated, we heard that former police and others who could gain access to surveillance systems were being hired by:
“law firms, telecoms giants and insurance companies … to hack, blag and steal private information to further their commercial interests.”
In short, once it’s available, it’s available to more people, and for more reasons, than you might assume.
So it’s safe to assume that, if this law is passed, yet more information about your virtual whereabouts and those of your sources will become fair game. And if you and a source are in the same virtual place at the same time, you have a problem.
I blogged earlier about HTTPS but that won’t protect you much in that situation. Tor and a Virtual Private Network (VPN) are where you need to look next.
As it happens, the Electronic Frontier Foundation have a very useful interactive graphic which shows you what information can be gathered by hackers, ISPs, police and lawyers when you browse the web without HTTPS or Tor, and what information is left when you do use either or both tools.

Pingback: How journalists can protect their sources from the snoopers » Binary Techniques Ltd
Pingback: How journalists can protect their sources from the snoopers | infopunk.org
Pingback: The Government wants to know where you were online, when. Why journalists should be cautious | Liquid Newsroom
Pingback: “Don’t be afraid: keep them afraid” and other notes from the Logan Symposium on surveillance’s first day | Online Journalism Blog
Pingback: Digital security tips for journalists: Protecting your sources and yourself - Journalist's Resource Journalist's Resource
Pingback: Digital security tips for journalists: Protecting sources and yourself - Security Insider Access Online
Pingback: Digital security tips for journalists: Protecting sources and yourself - NE Guard
Pingback: Digital security tips for journalists: Protecting sources and yourself - J-SIM