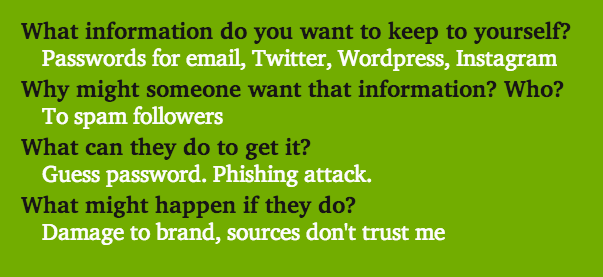
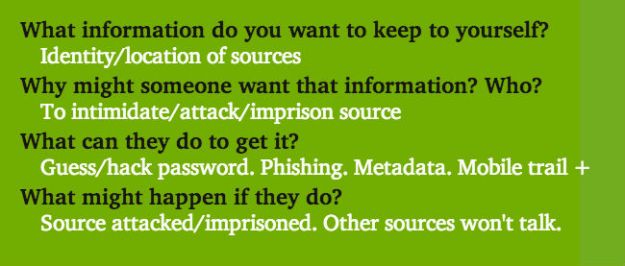
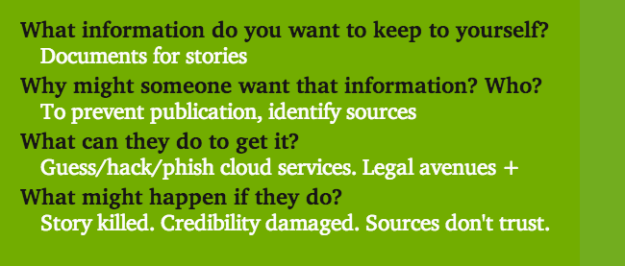
My post on threat models for journalists is quite lengthy, so I thought I’d put the sample threat models from that in their own, separate post. Here they are – note that these are very simple, sketchy threat models and you would want to expand on these. But hopefully they provide a starting point. I’d also recommend checking out this resource from Privacy for Journalists.
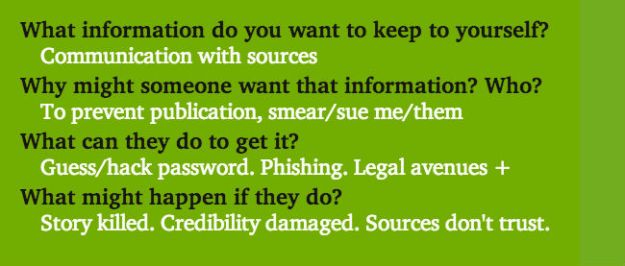
This is an example of a threat model for anyone who deals with protestors, complainants, or others who might be targets of others