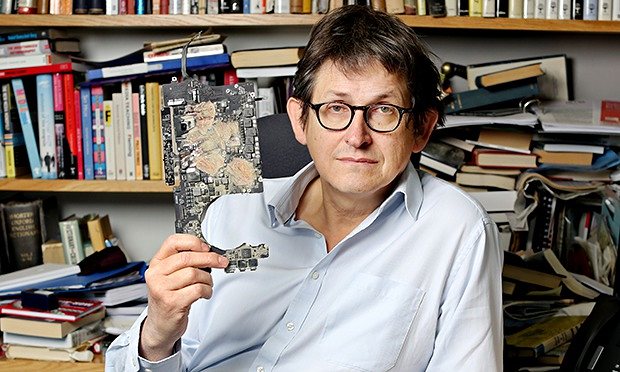
The Guardian complied when authorities demanded they destroy the Snowden files
So far most of the talk about the Investigatory Powers Bill has been about the lack of protection for journalists’ sources thrown up by powers to intercept communications.
But there’s another part to the Bill which relates to facilitating state hacking – and an analysis by Danny O’Brien has thrown up some worrying ambiguity on this front for publishers – not just those based in the UK.
The key here is how ‘communications providers’ are defined in the bill:
“The UK has redefined these terms so broadly that if you run an Internet company, administer a website, run an online video game, provision open source Internet software, operate a chat forum, or simply run a wifi hotspot, this power could be turned on you.”
Publishers, that means you.
Obliged to assist the authorities – and keep quiet
Why is this important? Because those covered by this definition are obliged by the law to assist with ‘hacking warrants’ (“equipment interference”) issued by the police, intelligence services, or tax and custom authorities. And they’re obliged not to tell anyone about it.
O’Brien lists just a few examples of what that might involve:
- “include in your web advertisement inventory a fake advert that pushes malware to a group of your readers;
- “roll out spyware to computers you have control over that would seize email, take screengrabs, pictures and record conversations;
- “push updates to software you’ve written, including a government-specified backdoor;
- “rewrite a smartphone app to relay its users’ position directly to the British authorities;
- “search through emails or other personal data you host, to find passwords or information that could help the authorities to hack;
- “create or fake messages to cause password resets or mislead users into accessing malware-infected website.”
This might sound alarmist, but it’s worth noting that publishers are already carrying malware in their ads. And one US agency has used fake news stories to plant malware on targets’ computers.
The future is already here: but is it just unevenly distributed?
Outsourcing without security
When combined with the mass collection of everyone’s data also proposed by the bill, the state would have the ability to identify not just an individual but a group of people by their online behaviour, identify the websites or apps they use, and then compel the publisher of that site or app to help hack the target.
This sounds incredible, and I hesitate to write it. Would an agency ever exercise those powers? Would a publisher comply?
Perhaps they would not even have to.
Outsourcing your app design or comment moderation, buying in a content management system or hosting content on a social media platform all represent potential security vulnerabilities when any of those third parties could be subject to the same warrants.
Trust
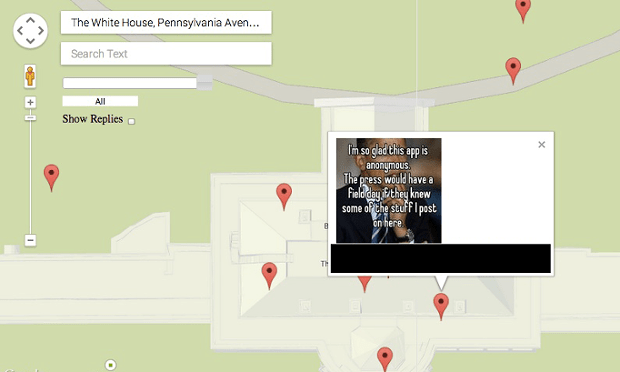
The app Whisper was revealed to be tracking users and sharing information with the Department of Defense
It is incredible. But so much in the last five years has been incredible. The Guardian, of course, complied when asked to destroy the Snowden files (an empty gesture, but still significant), and the misuse of RIPA powers by police and other public authorities has been shocking.
What is notable about the bill is that it affects anyone with a userbase above 10,000. That means not just brands with lawyers and political clout but also hyperlocal sites, niche publishers and fan forums. It includes this website.
It is not enough for former Attorney General Dominic Grieve to say the proposed bill is “well intentioned”. Surveillance has been justified on the grounds of protecting a public body’s interests; over employees’ breaking confidentiality clauses; or simply not justified at all. On other occasions confidential material has been handed over by accident.
When even the Chief Surveillance Inspector at the Office of Surveillance Commissioners says that “the legal and policy framework is not strict and that oversight is not rigorous”, we should worry.

GCHQ stored millions of Yahoo webcam images: this was Ampp3d’s take
At the bottom of all this lies our ability to build trust not only with sources, but with the audiences and communities we serve, and where sources live and work. This is the battle that Apple is having right now; that BlackBerry had in India. It is the reason that no one trusts Skype, or the Whisper app, or uses webcams on Yahoo.
For once the news industry has a chance to learn from the mistakes of the tech industry. We should not miss it. The NUJ has a briefing on what happens now, and the Open Rights Group has guidance on how to write to your MP.

Pingback: From Bana and #boycottdelta to gaslighting and AI – why we’re headed for confusion fatigue in 2017 | Online Journalism Blog
Pingback: How You Should Be Using Social Media to Resist tRump – Mindsworth
Pingback: Brave new world? 5 things your newsroom can do now to protect your journalism against the Snooper’s Charter | Online Journalism Blog