Category Archives: online journalism
Report: Journalism, media and technology predictions 2015
Last month I blogged about some reflections on 2014 I’d given to Nic Newman as part of his annual ring-round. Now his 39-page report on Journalism, media and technology predictions 2015 is live (PDF). Continue reading
3 ways to pitch ideas to an editor

Fitting into boxes. Image by David
How do you pitch ideas to editors as a journalist and get work? When I was asked this question recently I realised there tend to be three broad approaches. I may well have overlooked others – if so please let me know.
Plan A: Specialist knowledge and contacts
The most obvious way to pitch your journalistic services is to have something that others do not.
Anyone can review a film, rewrite a press release or interview a local MP. But not everyone has built good relationships with people who work in healthcare, or can get the person in charge of transport to return their calls, or knows who organises the local running club. Continue reading
FAQ: How Twitter has changed journalism; how journalism has stayed the same
This weekend’s FAQ comes from a journalism student who is writing her dissertation on the relevance of Twitter as a news source. As always I’m publishing my responses here in case anyone else has the same questions. Continue reading
2 quotes you need to read about Facebook’s video moves
“What the shift to Facebook video means is that Facebook is more interested in hosting the things media companies make than just spreading them, that it views links to outside pages as a problem to be solved, and that it sees Facebook-hosted video as an example of the solution. A company that uploads its videos to Facebook is not the publisher of those videos. At best, it produced them. Continue reading
What to do if your FOI is refused under ‘commercial sensitivity’ and ‘breach of confidence’
If you’re using FOI to ask questions about public services involving private companies it’s quite common to be refused on the basis of ‘commercial sensitivity‘ or ‘breach of confidence‘.
In fact, I’d suggest anticipating this in your initial request – or at the very least pushing for details when you receive any initial refusal.
Both exemptions are often misused by authorities as a ‘catch-all’ reason to fob off a requestor.
But neither exemption is simple, and both have a public interest test element which the authority is supposed to have thought through. In brief there are two things you can do to help your request: Continue reading
2 weeks to “Save journalists’ sources” in consultation over law used to spy on journalists
2014 was the year journalists found out just how widely the Regulation of Investigatory Powers Act (RIPA) was being used by public authorities to spy on reporters and identify their sources.
Two years earlier political editor Tom Newton Dunn had refused to co-operate with officers on his sources for a story despite being threatened with arrest himself.
So the police obtained his mobile phone records and call data to his newsdesk. His sources, identified from the logs, were then sacked.
Since we have heard The Spectator’s Nick Cohen report that “the police now tell journalists that they have [used the RIPA Act to pull] reporters’ phone records in every single leak inquiry in the last ten years.”
Press Gazette’s William Turvill has reported on the council that used RIPA to spy on a local journalist’s meeting with a member of staff.
And he has also reported on RIPA’s possible involvement in “allegations of improper seizure of journalistic material … from a Sky News journalist.”
Two things to do
This month, you can do two things about that.
Firstly, you can sign Press Gazette’s petition to ‘Save Our Sources’ which asks the Home Secretary to:
“find out how many times public authorities have used RIPA to obtain the phone records of journalists and to ensure new guidelines are in place to prevent this happening in future.”
Secondly, there is a rare opportunity to contribute to a government consultation on RIPA.
The NUJ have helpfully provided all the details on their call to members to respond, including a template letter.
There are two weeks to get your letter in: the deadline is Tuesday 20 January 2015.
Send them via email to: commsdata@homeoffice.x.gsi.gov.uk
When reporting on data remember that those who don’t count aren’t counted

Invisible man image by Brian
In a guest post for OJB, Help Me Investigate contributor Natalie Leal talks about how statistics on benefit claimants, migrants and A&E admissions reflect organisations’ priorities – and can be skewed as a result.
I recently witnessed an unemployed woman at a job centre shouting that she would “never ever” set foot in there again.
The woman, who had just been told that her benefits would be cut off for thirteen weeks, stormed past two security guards on her way out.
They turned to each other and joked:
“That’s another one off the books.”
The 10 most-read posts (and one page) on the Online Journalism Blog in 2014
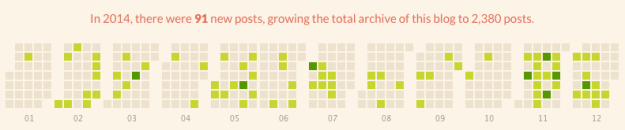
The last 2 months of 2014 saw a return to regular blogging after some quiet periods earlier in the year
2014 was the 10th anniversary of the Online Journalism Blog, so I thought I’d better begin keeping track of what each year’s most-read posts were.
In 2014 the overriding themes for this blog were programming for journalists, web security, and social media optimisation. Here are the most-read posts of the year, plus one surprisingly popular new page with some background and updates. Continue reading
This Christmas, encrypt your emails and make the haystack bigger
Why should journalists be interested in web security? You may not fear your social media accounts being hacked by propagandists, your email hacked by companies you write about, or your phone records being seen by police, but there is another good reason for adopting security measures.
“Anonymity loves company,” security researcher Ross Anderson reminded attendees at this month’s Logan Symposium on secrecy, surveillance and censorship. “You can only hide in a crowd.”
In other words, the more people who use encryption in their email, or other security measures, the less unusual it becomes.
And the more widespread these practices are, the harder it is for the contents of messages to be used to identify whistleblowers – whether that is with journalists, charities, or even whistleblowing services (remember that only the message is encrypted, not the identity of the sender or recipient).
So if you have some spare time over the festive period, why not get yourself set up with an email client like Thunderbird with a plugin like Enigmail, and get started.